How to Build a No-Code Ransomware Recovery Tool – A Complete Guide. Ransomware attacks are one of the most significant cybersecurity threats today. Many organizations struggle with recovery due to complex coding requirements and insufficient IT resources. Fortunately, no-code cybersecurity tools allow businesses to implement ransomware recovery automation without needing specialized programming skills. In this article, we’ll explore How to Build a No-Code Ransomware Recovery Tool using practical strategies, automated workflows, and low-code platforms.
Why Businesses Need a No-Code Ransomware Recovery Tool
Ransomware attacks can cripple businesses, causing data loss, financial damage, and reputational harm. Traditional recovery methods often require skilled developers and time-consuming coding processes. By using no-code workflow automation for security, organizations can:
- Quickly recover files after ransomware attack
- Implement automated ransomware detection and recovery
- Maintain business continuity with minimal IT intervention
A ransomware data recovery solution built with no-code tools allows both technical and non-technical teams to manage recovery efficiently.
Key Features of a No-Code Ransomware Recovery Tool
Before learning How to Build a No-Code Ransomware Recovery Tool, it’s essential to understand the core features such tools should include:
| Feature | Description | Benefit |
|---|---|---|
| Automated Backups | Periodic backups of endpoints and servers | Enables faster ransomware recovery |
| Threat Detection | Integration with low-code incident response platform | Immediate alert on ransomware activity |
| Data Restoration | Restore files from backups with one click | Reduces downtime and data loss |
| Workflow Automation | No-code IT disaster recovery tools | Allows teams to manage recovery without coding |
These features ensure your system is prepared for ransomware attacks while simplifying the recovery process.
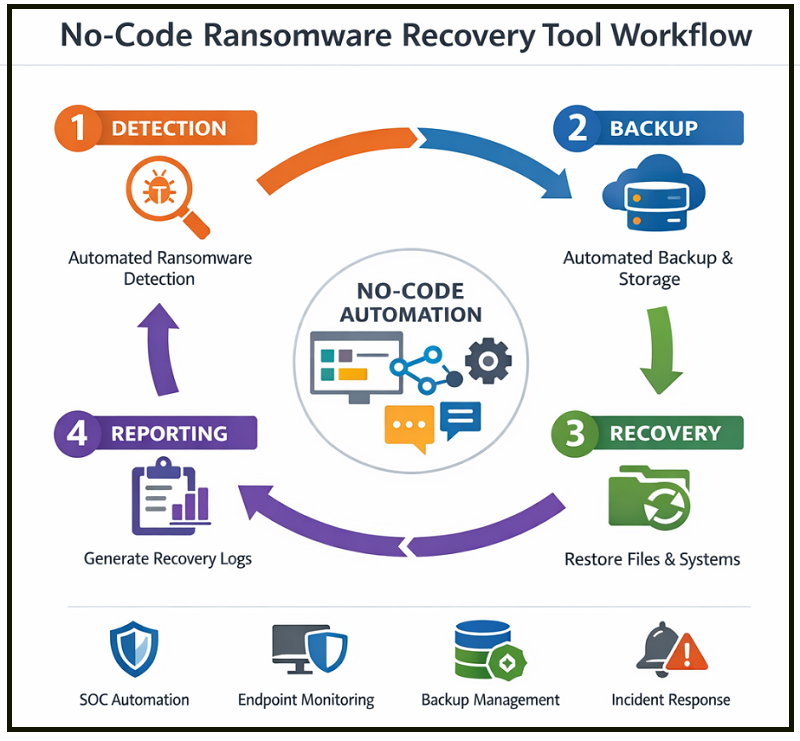
Step-by-Step Guide: How to Build a No-Code Ransomware Recovery Tool
Step 1: Choose the Right No-Code Platform
Selecting a robust platform is the first step. No-code SOC automation platforms like Zapier, Integromat, and Microsoft Power Automate provide pre-built security templates that support ransomware response and remediation.
Key considerations:
- Integration with your backup system
- Support for automated ransomware detection and recovery
- Pre-built triggers for endpoint ransomware recovery process
Step 2: Map Your Recovery Workflow
After selecting a platform, define the recovery workflow. This includes how files are backed up, detected as encrypted by ransomware, and restored.
| Workflow Stage | No-Code Automation Task | LSI Keyword Integration |
|---|---|---|
| Detection | Use automated triggers for ransomware | automated ransomware detection and recovery |
| Backup | Connect cloud or local storage | backup and restore automation tools |
| Restoration | Auto-restore encrypted files | recover files after ransomware attack |
| Reporting | Generate recovery logs | ransomware mitigation and prevention |
This step ensures that ransomware recovery automation is seamless and requires minimal manual intervention.
Step 3: Integrate Backup and Restore Systems
A ransomware data recovery solution is incomplete without reliable backups. Using no-code IT disaster recovery tools, you can schedule backups, monitor file integrity, and restore data automatically.
Pro Tip: Incorporate both local and cloud backups to safeguard against severe attacks.
Step 4: Automate Detection and Response
A key element of How to Build a No-Code Ransomware Recovery Tool is automated ransomware detection and recovery. Use the platform to:
- Scan endpoints for suspicious activity
- Trigger workflows to isolate infected machines
- Restore affected files from secure backups
| Detection Method | Tool | Benefit |
|---|---|---|
| File Encryption Monitoring | Low-code incident response platform | Rapidly identifies ransomware attack |
| Endpoint Threat Scanning | No-code SOC automation | Reduces risk of lateral spread |
| Scheduled Audits | No-code workflow automation for security | Ensures consistent monitoring |
Automation reduces response time and prevents the ransomware from spreading.
Step 5: Test and Optimize Your Recovery Tool
Testing is crucial to ensure your no-code ransomware recovery tool works as intended. Simulate ransomware attacks and check the restoration process. Analyze logs for gaps and refine the workflow.
- Use ransomware mitigation and prevention strategies during testing
- Ensure cyberattack recovery without programming is possible
- Adjust backup frequency and detection thresholds
A well-tested tool can save significant time and resources during real attacks.
Advantages of a No-Code Approach
| Advantage | Explanation | LSI Keyword |
|---|---|---|
| Speed | Quickly deploy recovery solutions | build security tools without coding |
| Accessibility | Non-developers can manage workflows | no-code cybersecurity tools |
| Cost-Effective | Reduces need for IT resources | low-code incident response platform |
| Flexibility | Easily modify workflows | no-code workflow automation for security |
This approach democratizes cybersecurity and empowers organizations to handle ransomware recovery efficiently.
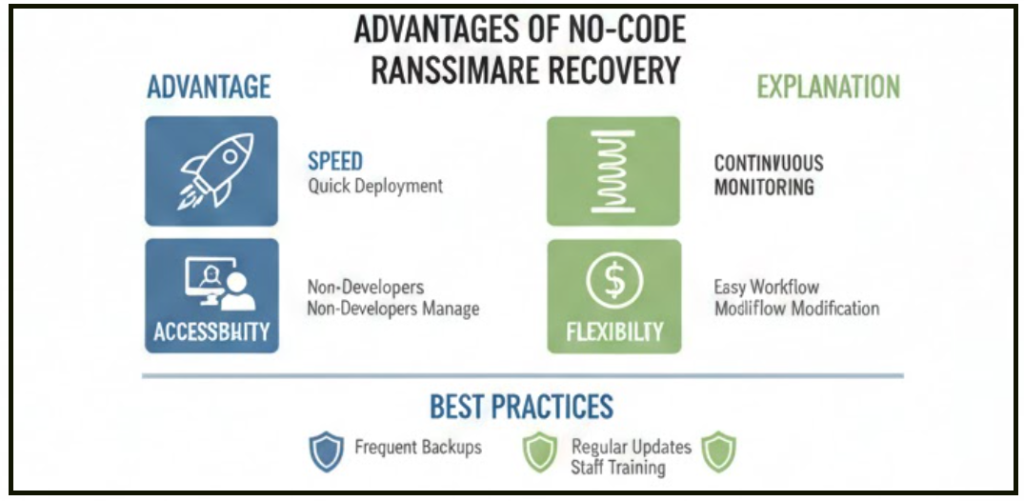
Best Practices for Ransomware Recovery Automation
- Maintain frequent backups using backup and restore automation tools
- Regularly update your no-code IT disaster recovery tools
- Monitor endpoints continuously with automated ransomware detection and recovery
- Document workflows for ransomware response and remediation
- Train staff on recover files after ransomware attack procedures
By implementing these best practices, businesses can minimize downtime and data loss during cyberattacks.
Small FAQ Section
Q1: Can I build a ransomware recovery tool without programming?
Yes. Using no-code cybersecurity tools and workflow automation platforms, you can implement cyberattack recovery without programming.
Q2: How effective are no-code tools in ransomware recovery?
No-code platforms offer automated ransomware detection and recovery, which reduces response time and prevents the spread of malware.
Q3: Do I need multiple platforms for complete recovery?
Not necessarily. Many platforms provide low-code incident response platform features, backup and restore automation tools, and no-code SOC automation within one ecosystem.
Conclusion
Learning How to Build a No-Code Ransomware Recovery Tool is critical for businesses facing increasing cyber threats. By leveraging no-code workflow automation for security, organizations can implement ransomware recovery automation, recover files after ransomware attack, and maintain business continuity without specialized coding skills.
With a proper combination of no-code IT disaster recovery tools, automated monitoring, and workflow optimization, building a secure and effective ransomware recovery solution has never been easier.